Cisco Duo with ASA AnyConnect
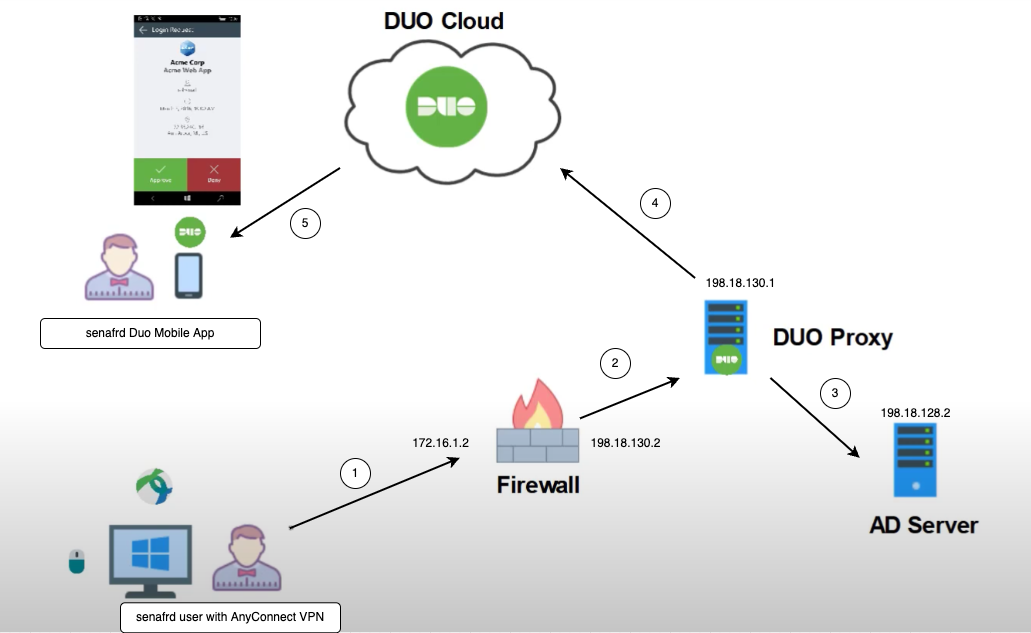
Cisco Duo integrates with ASA’s AnyConnect VPN to provide MFA (Multi-Factor Authentication) for secure remote access. When a user logs in to the AnyConnect VPN client, Duo’s authentication process is triggered, typically after the primary credentials are validated against an Active Directory. Duo pushes a second factor, such as a mobile app notification, SMS, or phone call, to the user for verification to add an additional layer of security for VPN access.
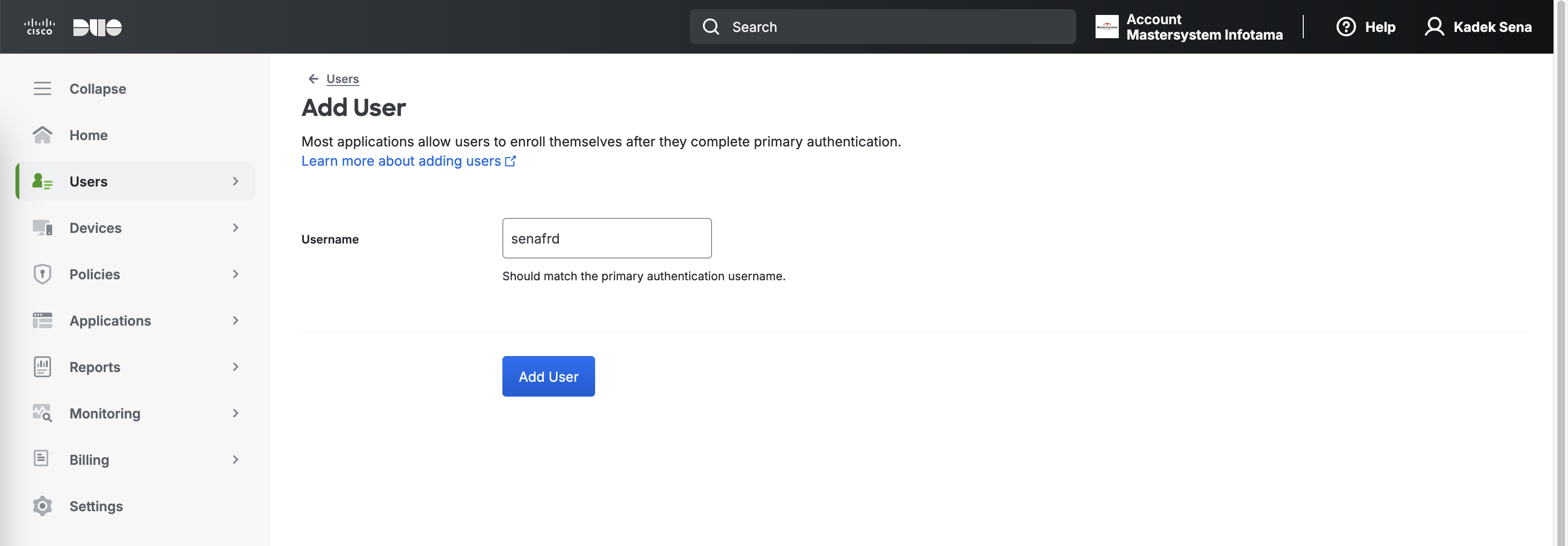
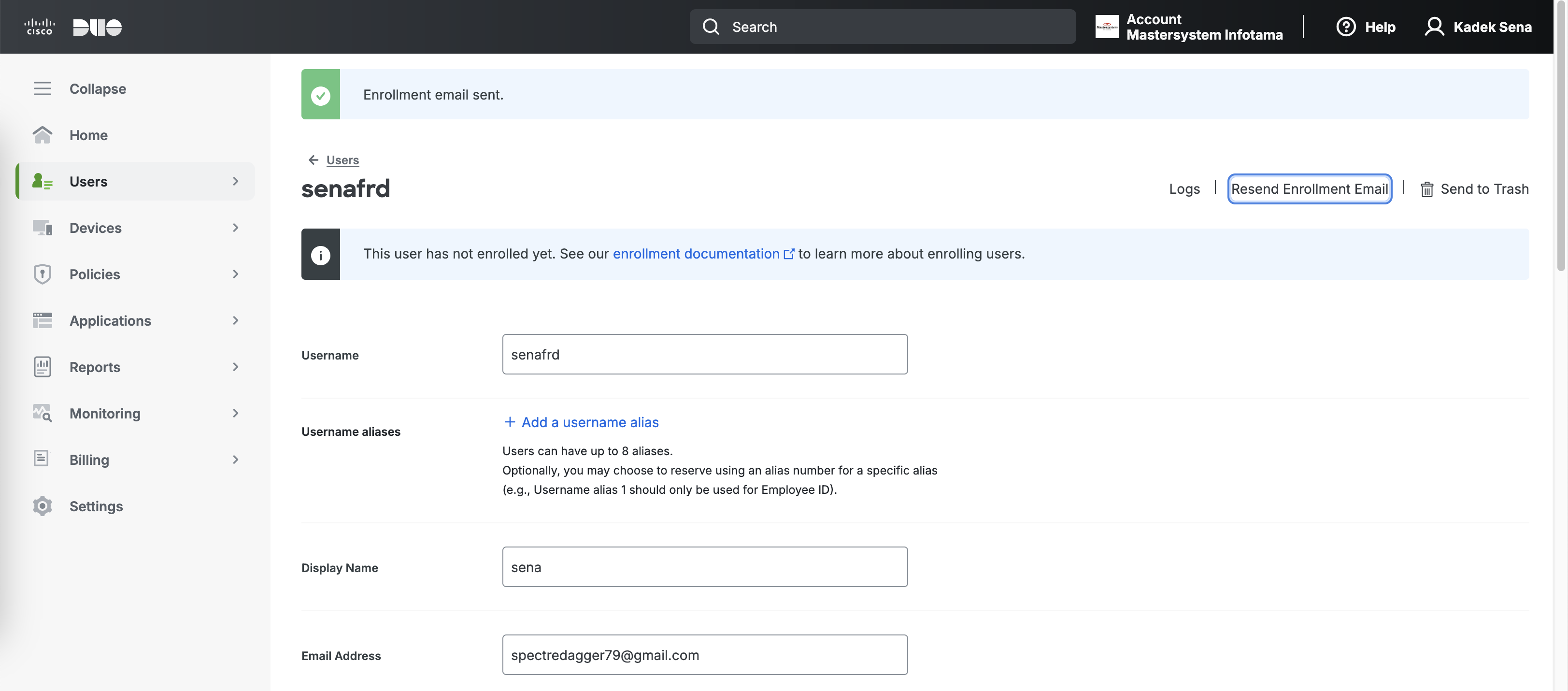
Creating User
On the Duo Admin Portal, create a User, this user has to be present on the Local Active Directory
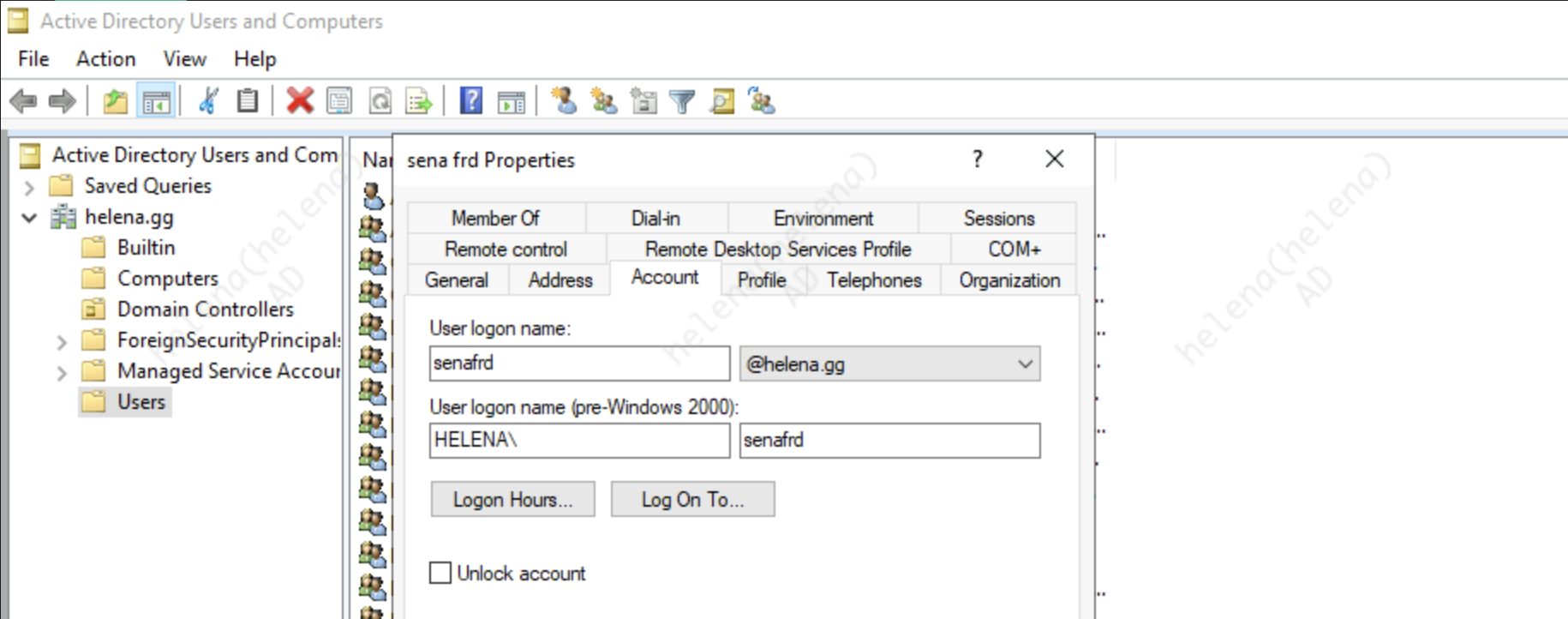
Here’s the user with the same name on the AD side
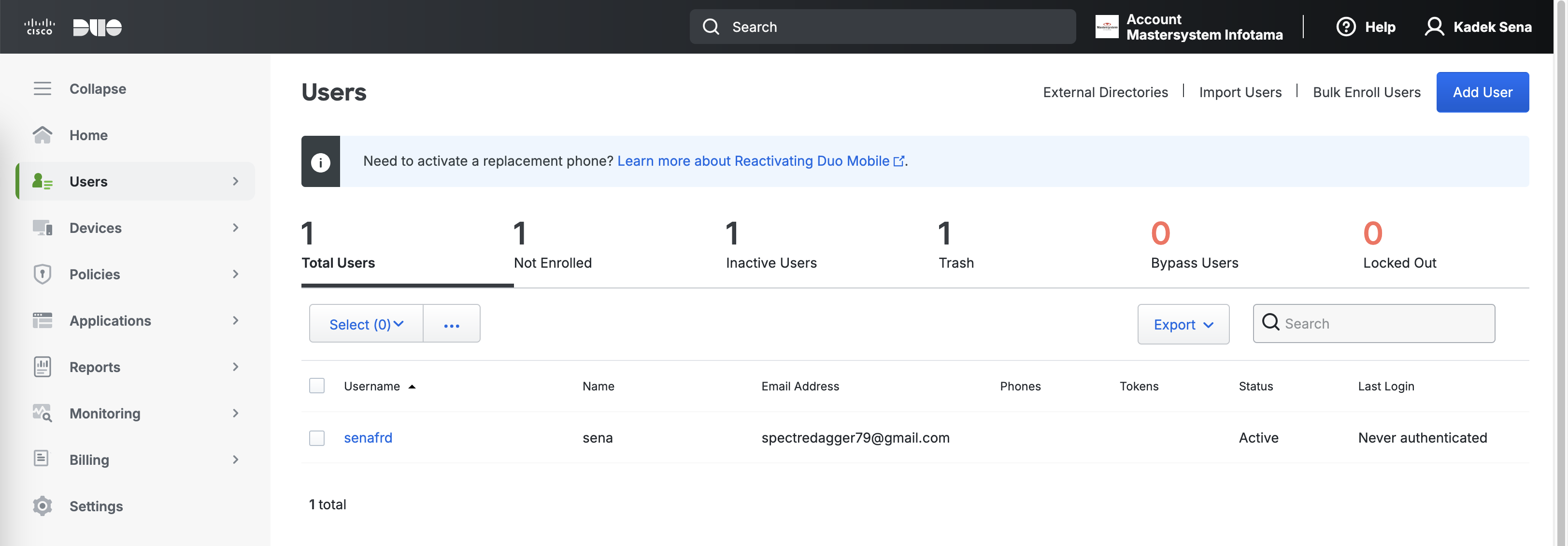
Now the user is made with correct email, notice that it’s active but the status is Not Enrolled
Select the user and hit “Send Enrollment Email” to enroll the user
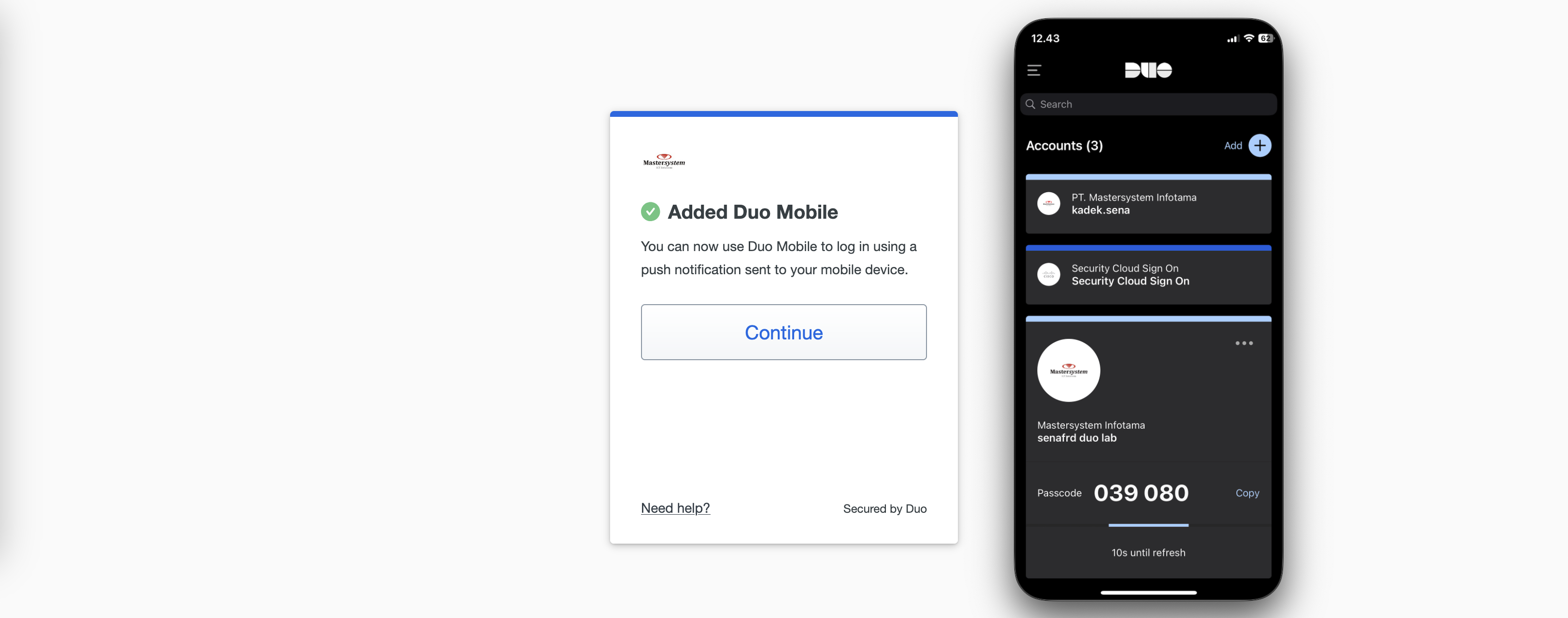
On the user end, we can click the link sent to the email and add the account to the Duo Mobile App
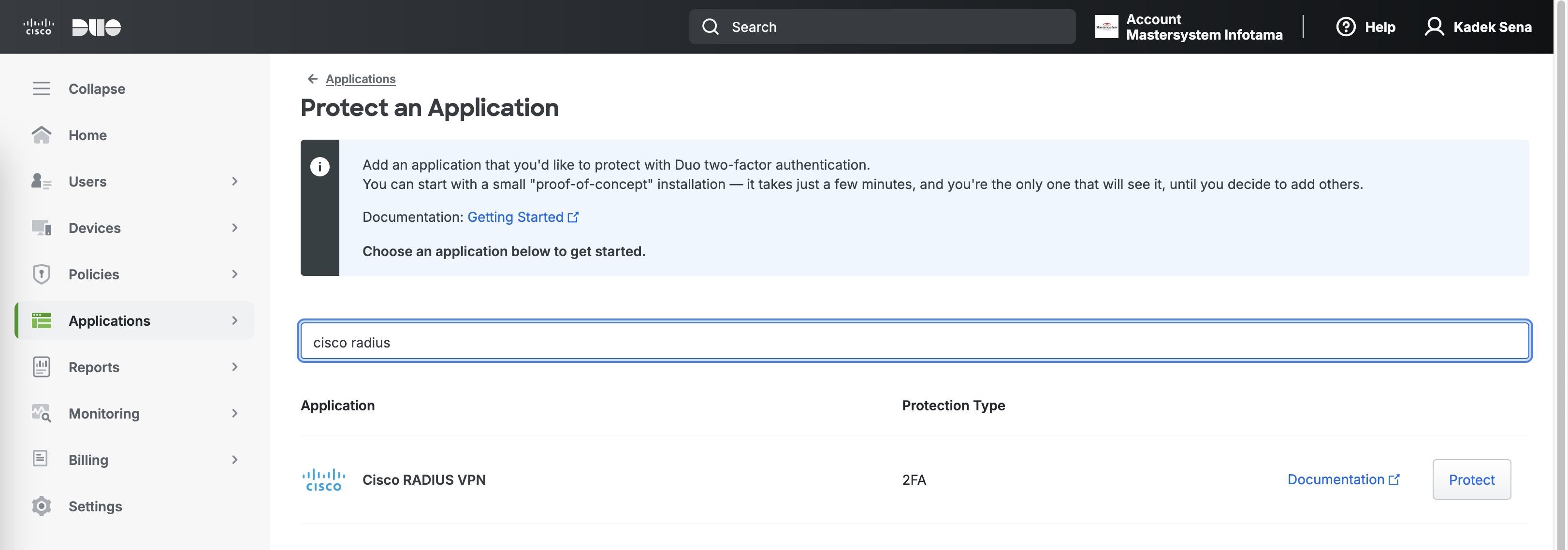
Protecting Application
Next select Protect Application, and search for Cisco Radius VPN
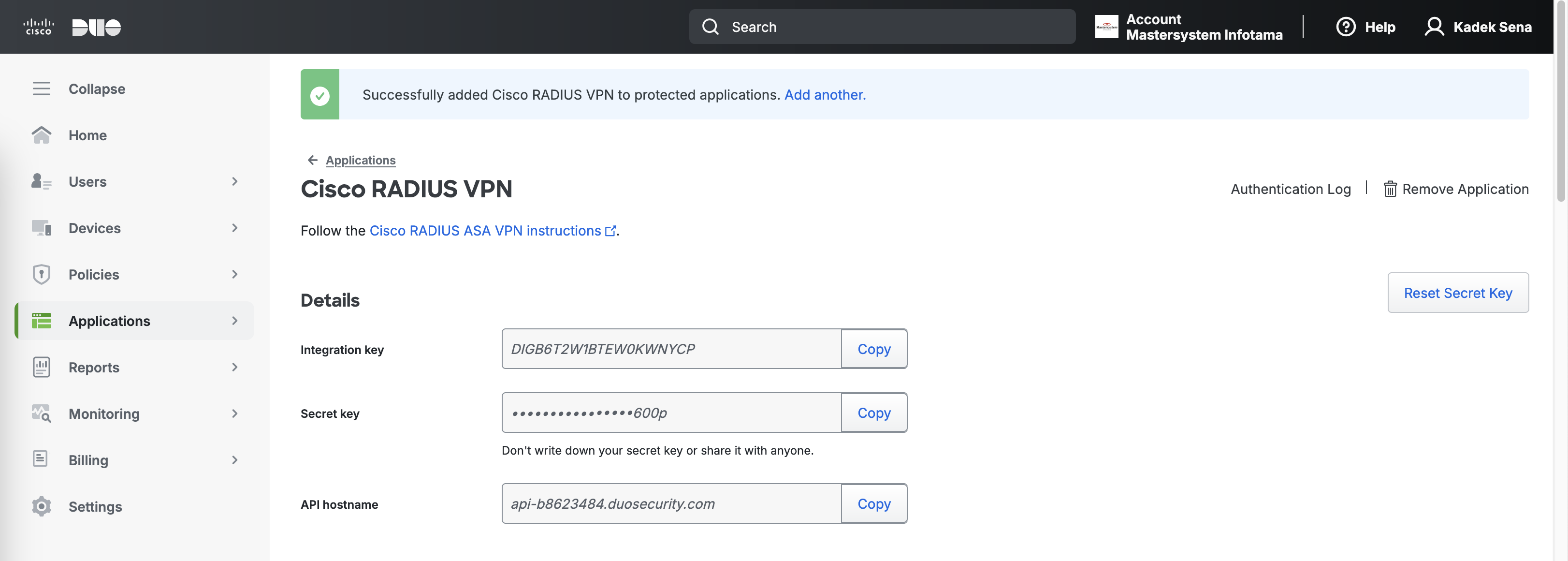
Upon creating the App, we’ll be given some keys and an API hostname, keep it stored for later configuration
Installing Duo Proxy Autentication Server
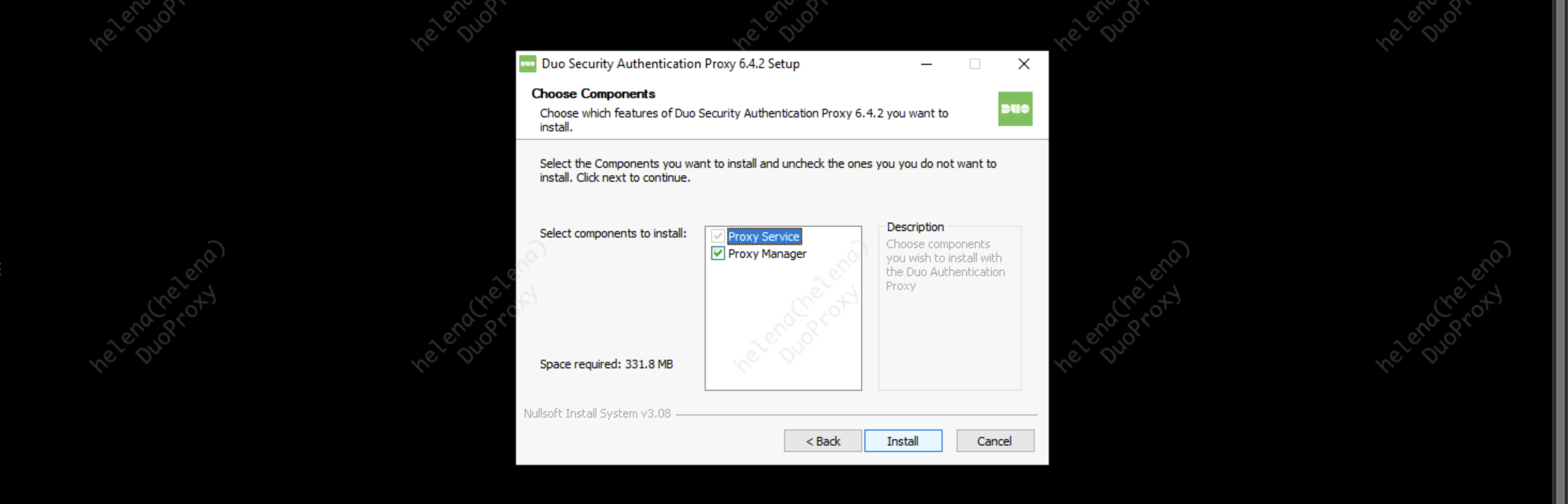
On a freshly installed Windows Server, download the Duo Auth Proxy Installer and run it
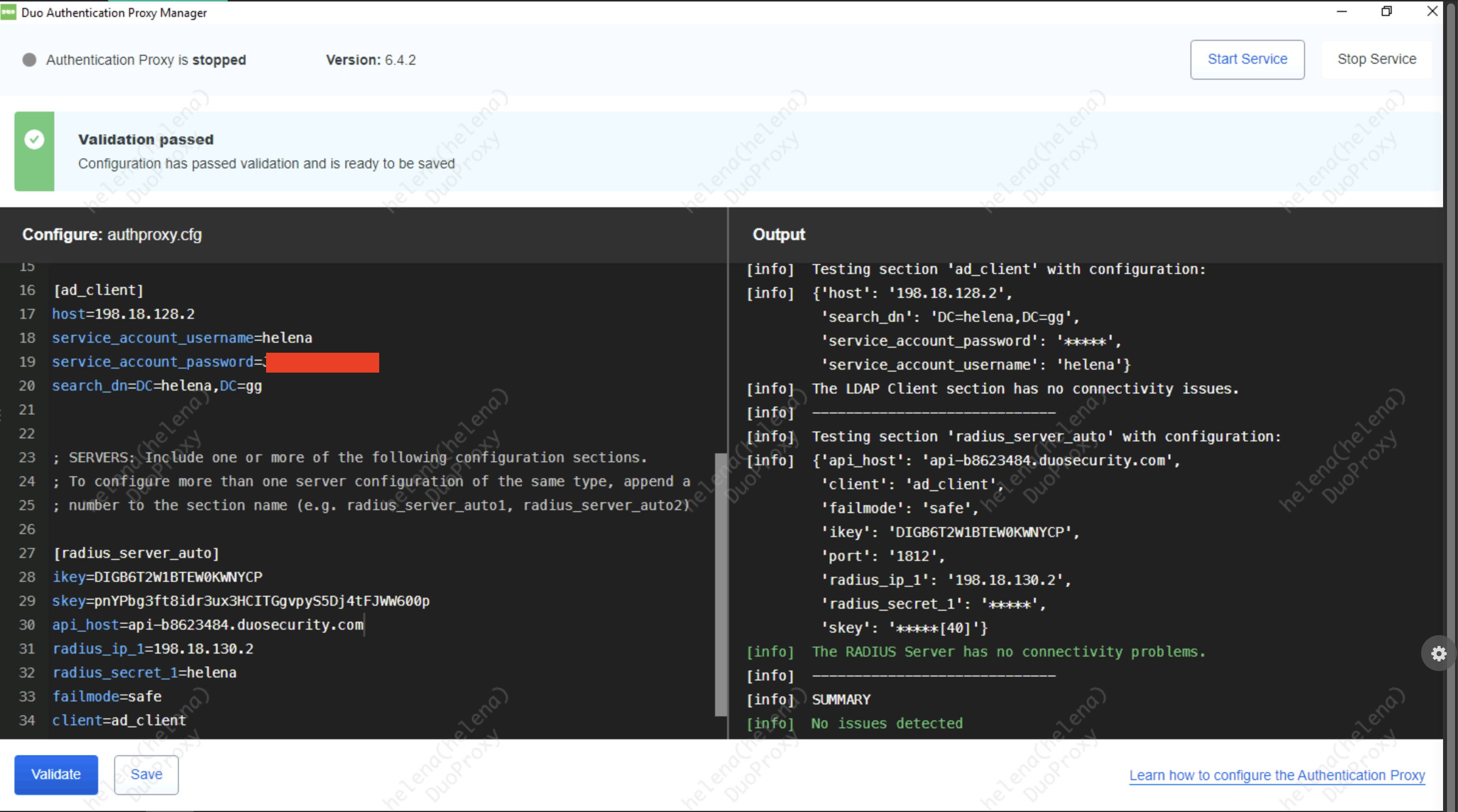
Then open the Proxy Manager and configure the authproxy.cfg, hit Save and select Validate to confirm everything is nominal
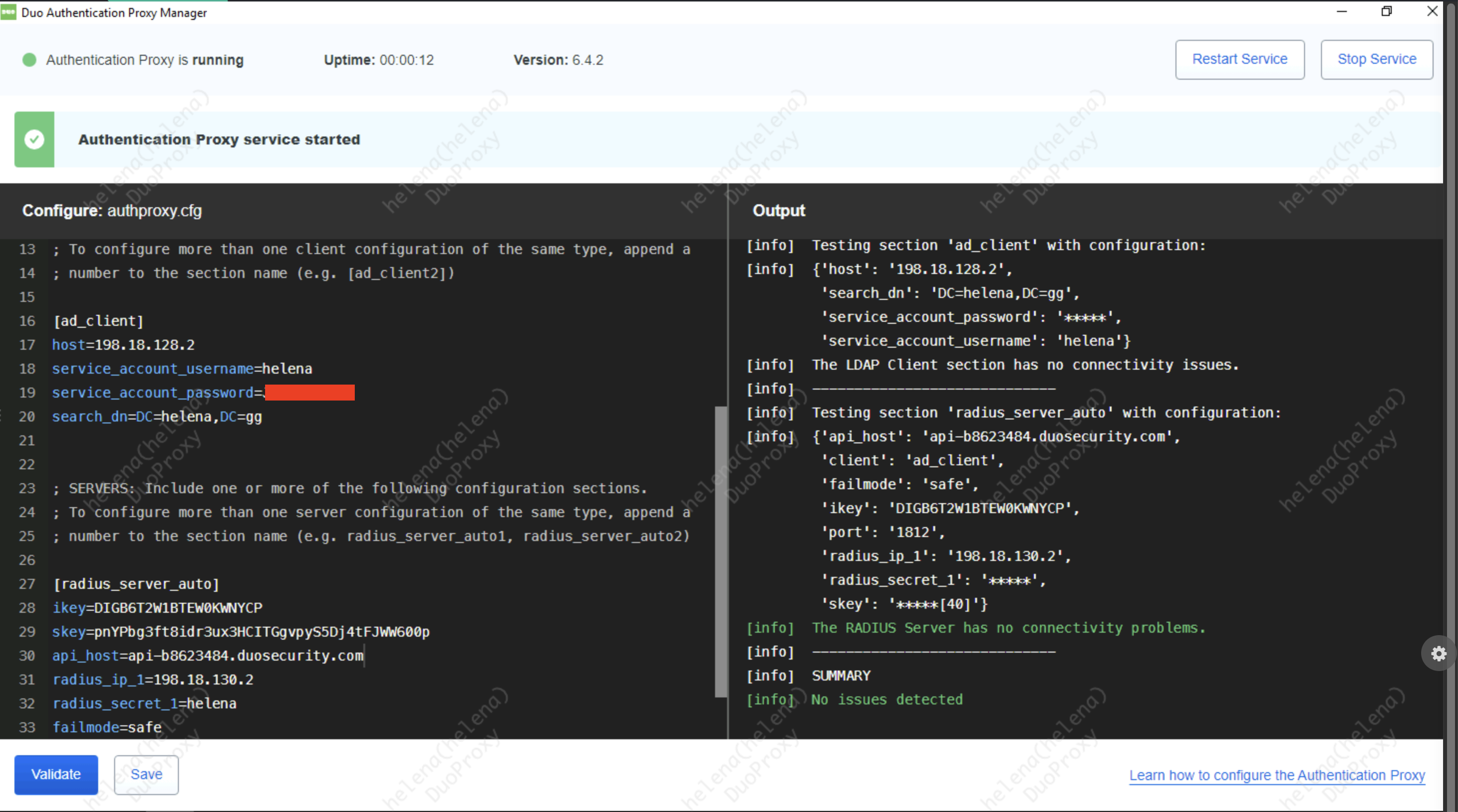
After that, select Start Service to start the Proxy
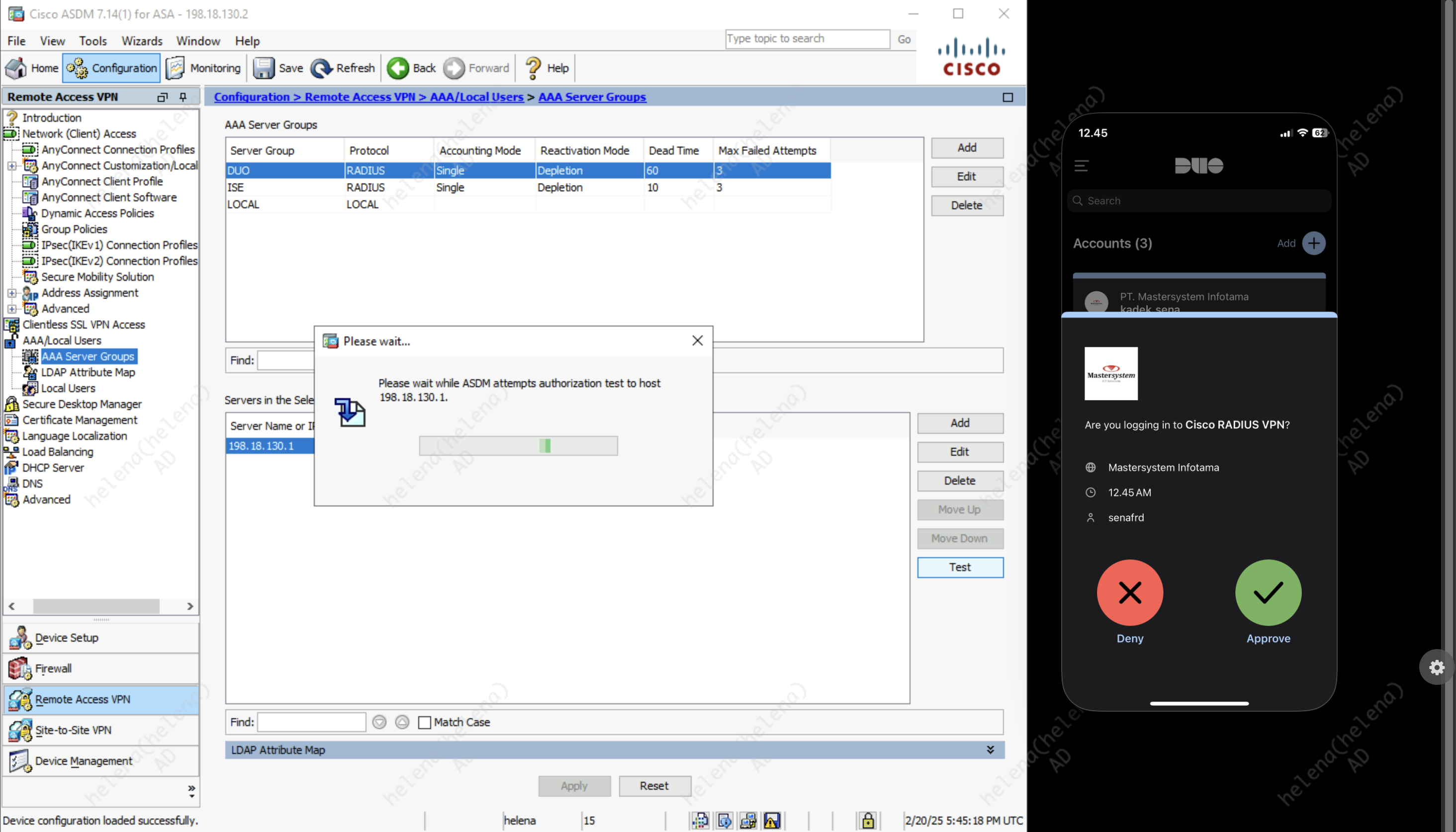
ASA Configuration
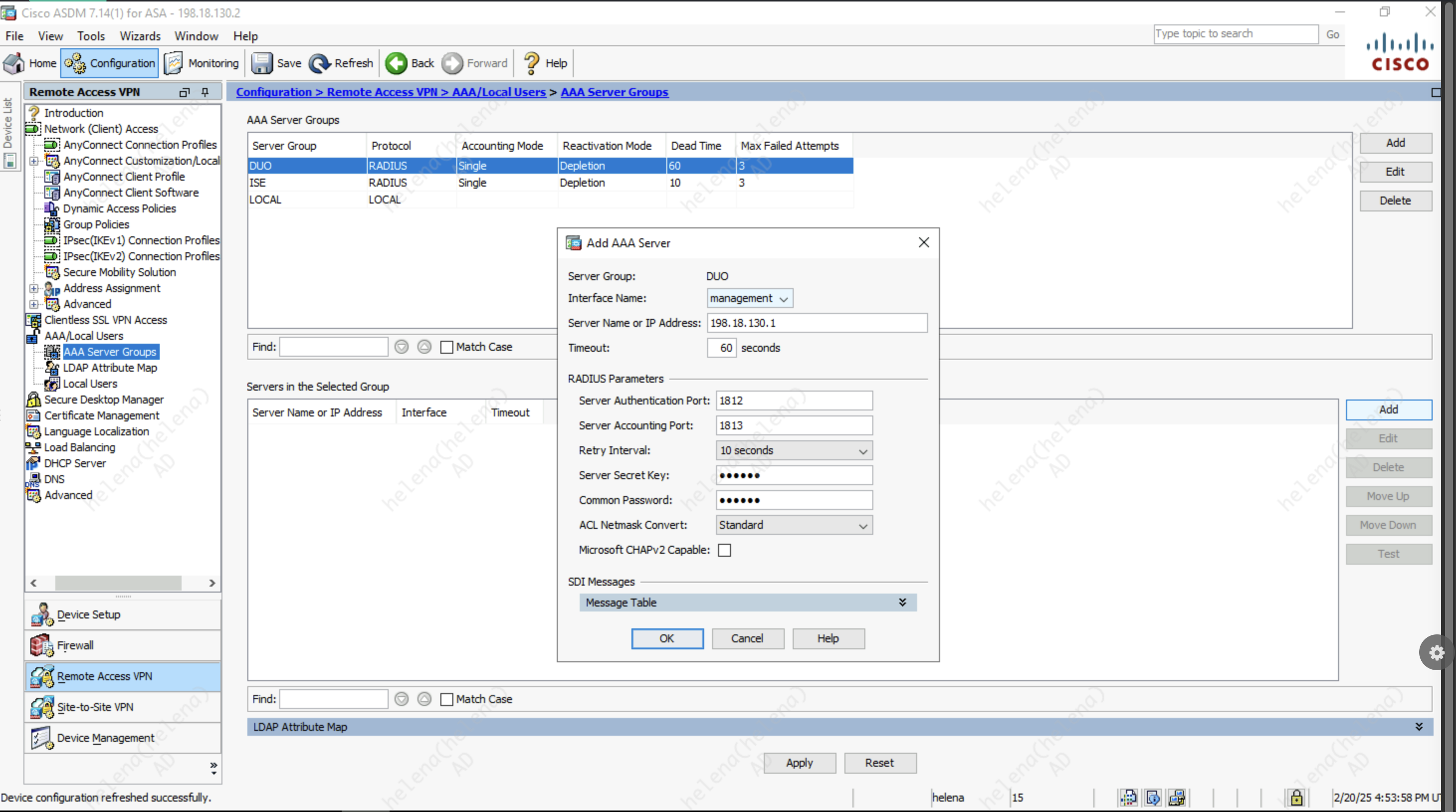
On ASA, we’ll add the Duo Proxy Server as an AAA Radius Server
After that, we can run the authentication test using the “senafrd” user, we should receive MFA confirmation on our Duo Mobile App
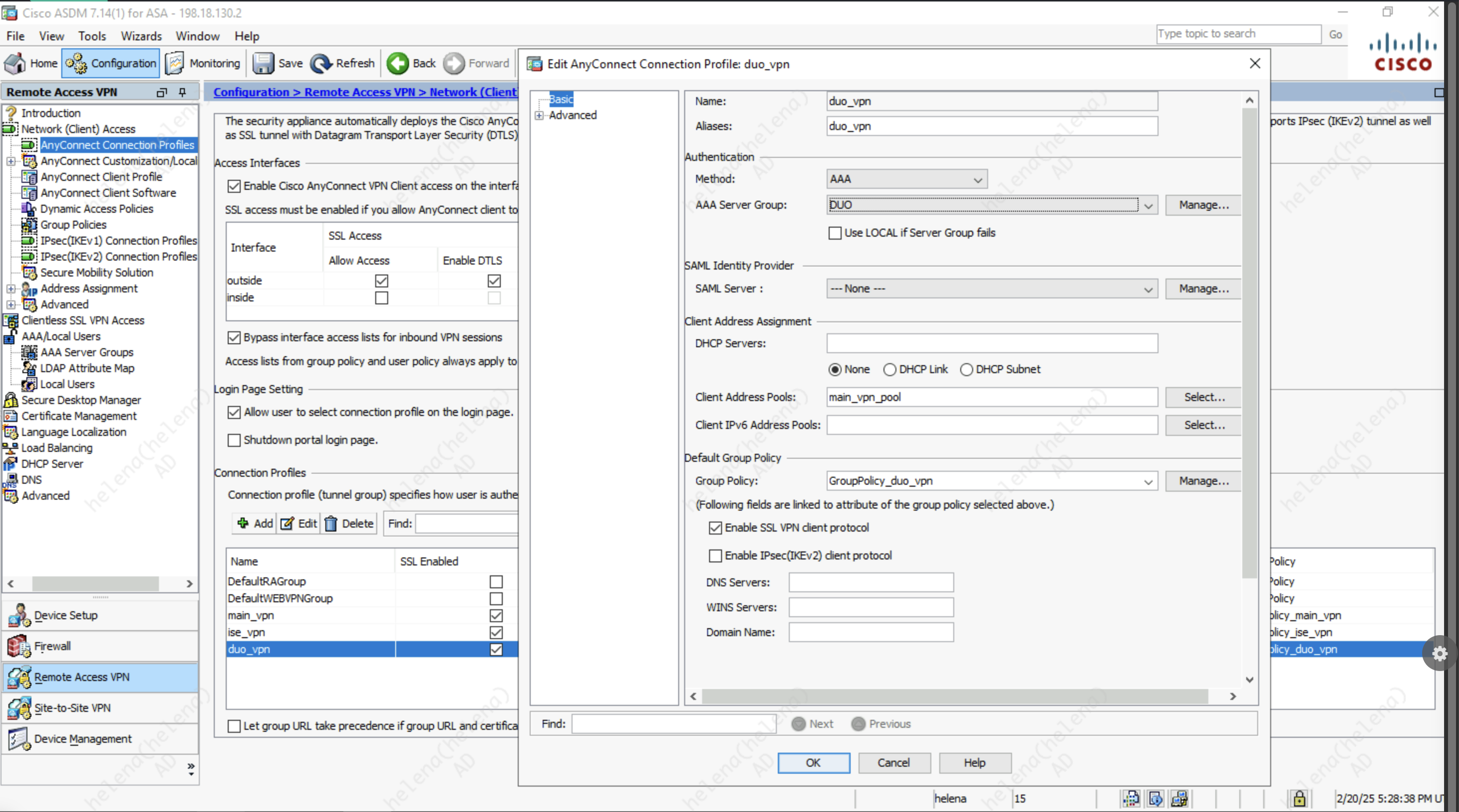
Now we can select the Duo as the AAA Server Group on the VPN Connection Profiles
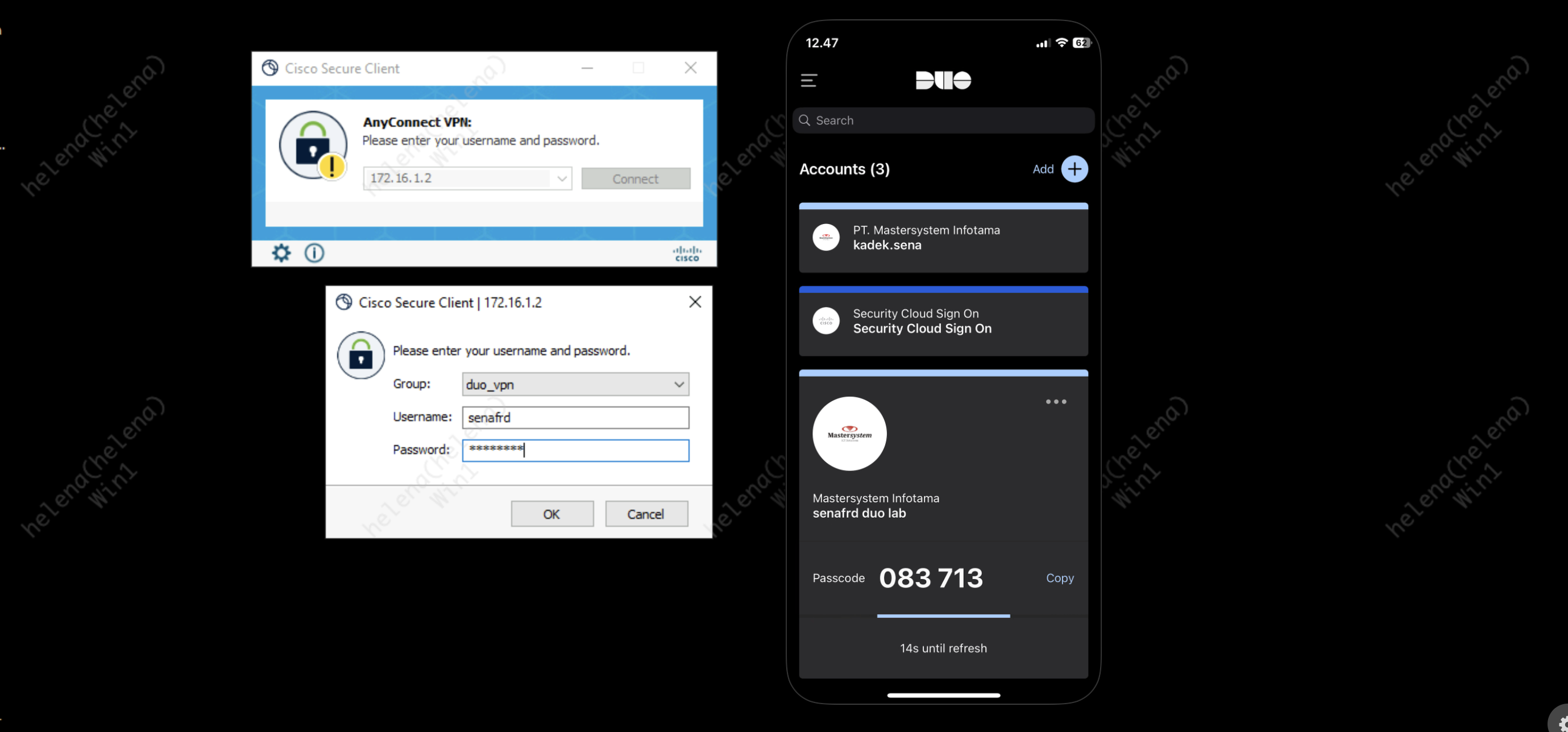
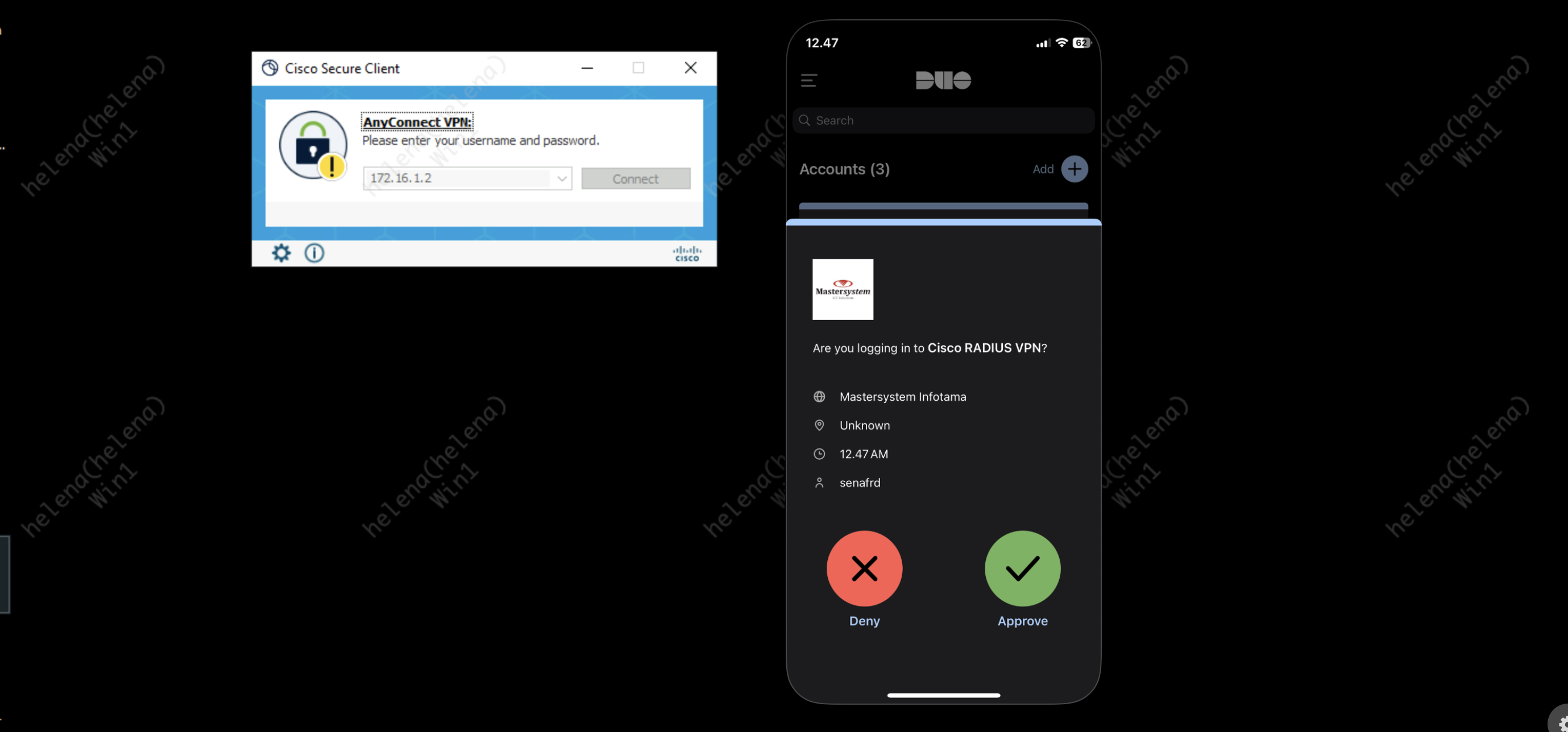
And finally when we try connecting to VPN, we’ll get the MFA confirmation on the App
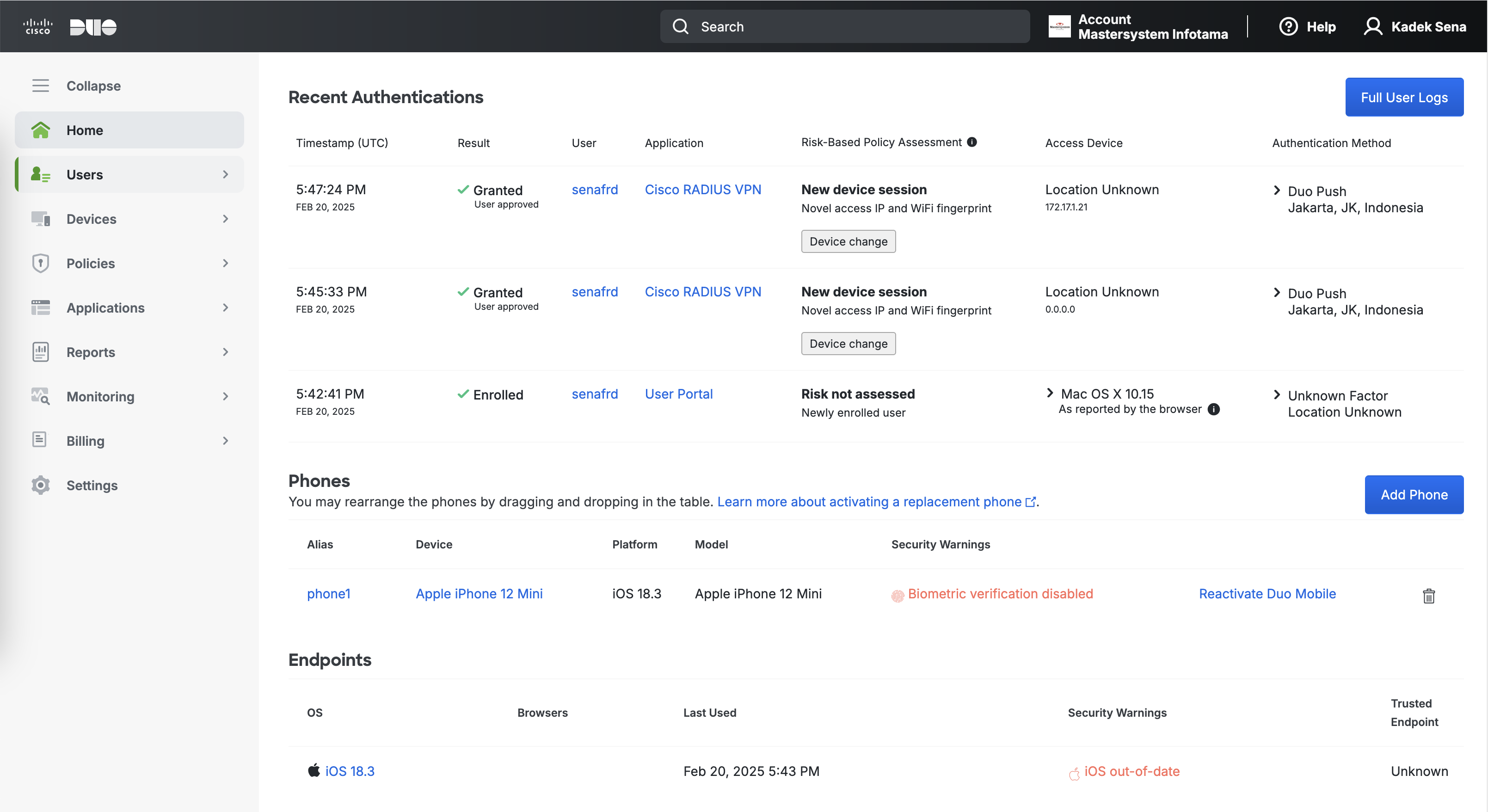
On the Duo Admin Portal, we can see the Authentication History and Endpoints used by this “senafrd” user