Cisco Duo with ISE
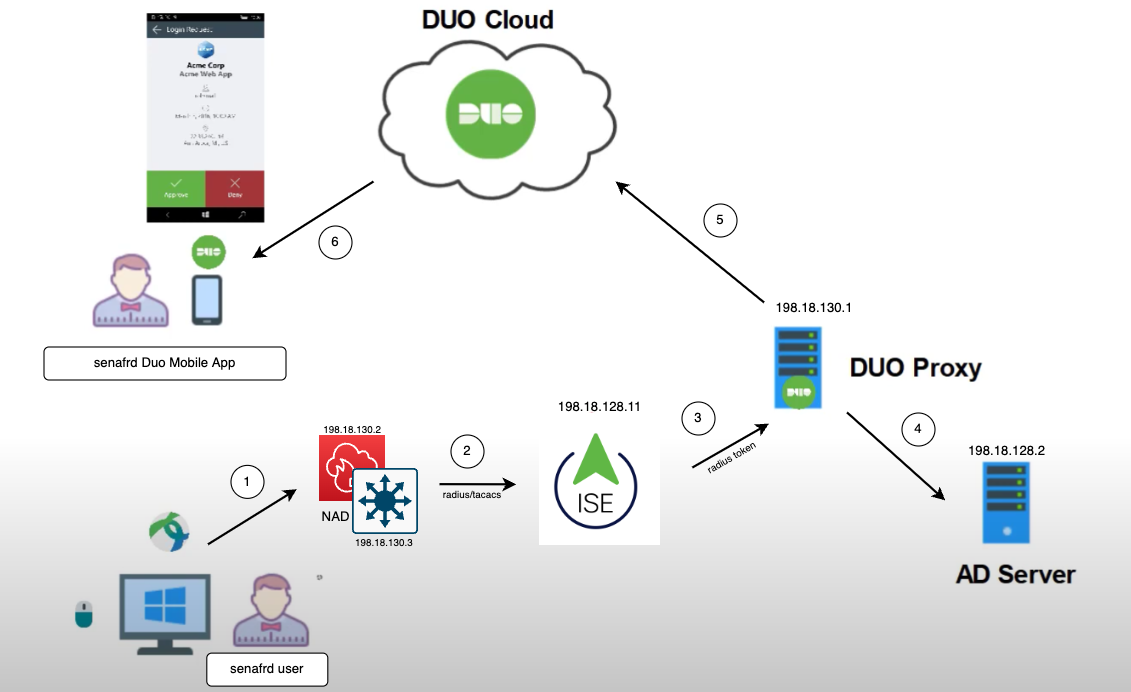
Cisco Duo integrates with Cisco ISE to enable Multi-Factor Authentication (MFA) for network access. The integration involves configuring Cisco ISE as a RADIUS client for Duo’s Authentication Proxy, which acts as an intermediary between ISE and Duo’s cloud service. When a user attempts to authenticate, ISE forwards the authentication request to the Duo Authentication Proxy, which validates the primary credentials to Active Directory. If successful, Duo triggers a second-factor authentication to the user. Upon successful MFA, ISE grants network access based on the configured policies.
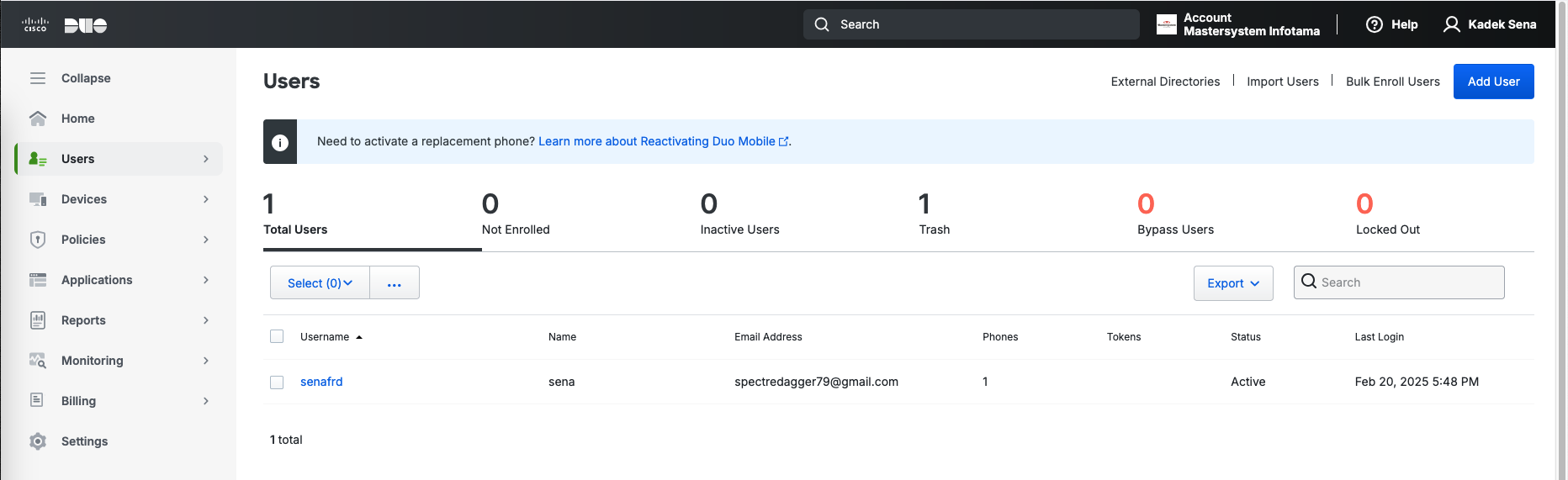
Duo Admin Portal
Everything configured here is continuing from this Cisco Duo and ASA AnyConnect Integration post, here on the Cisco Duo Admin Portal we make sure that the user is present
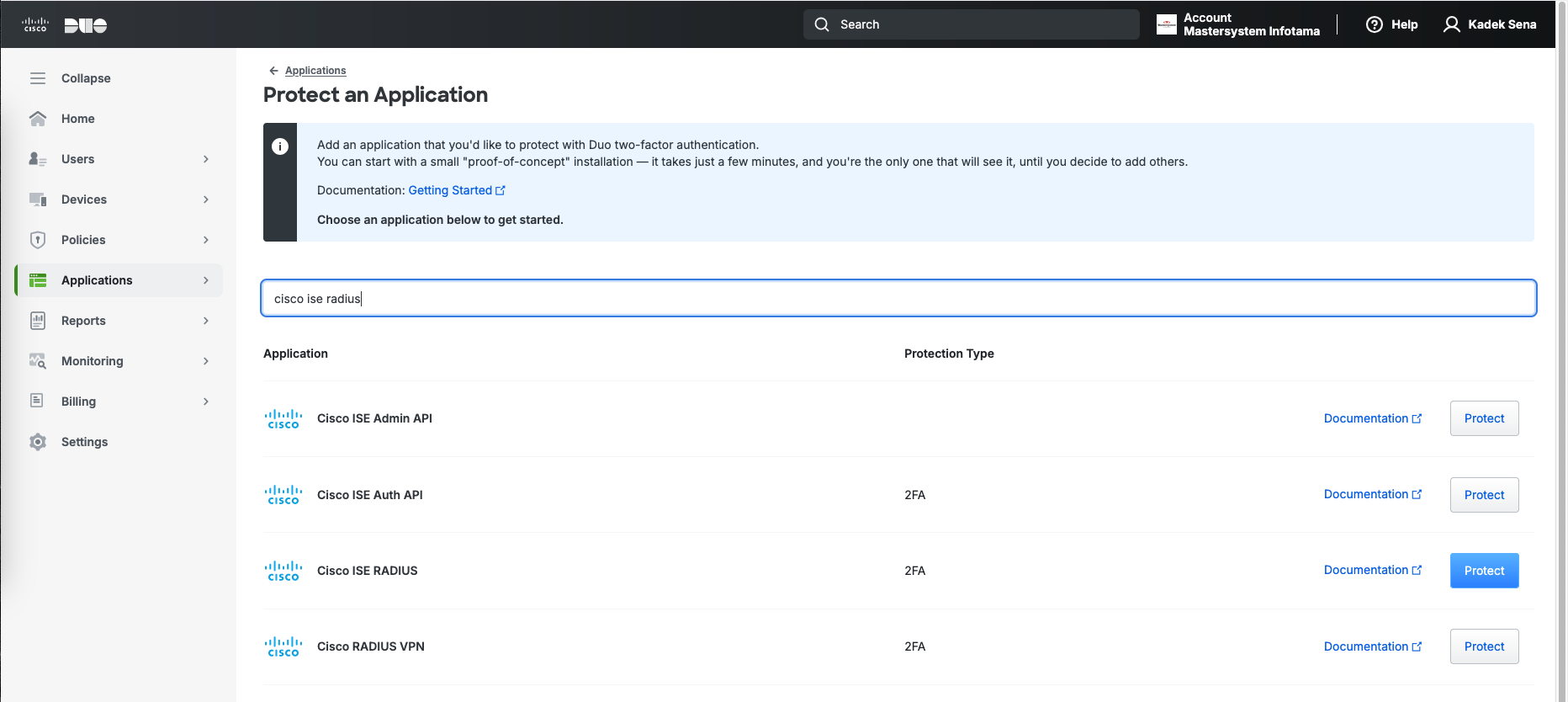
Then we add another Application to protect named “Cisco ISE Radius”
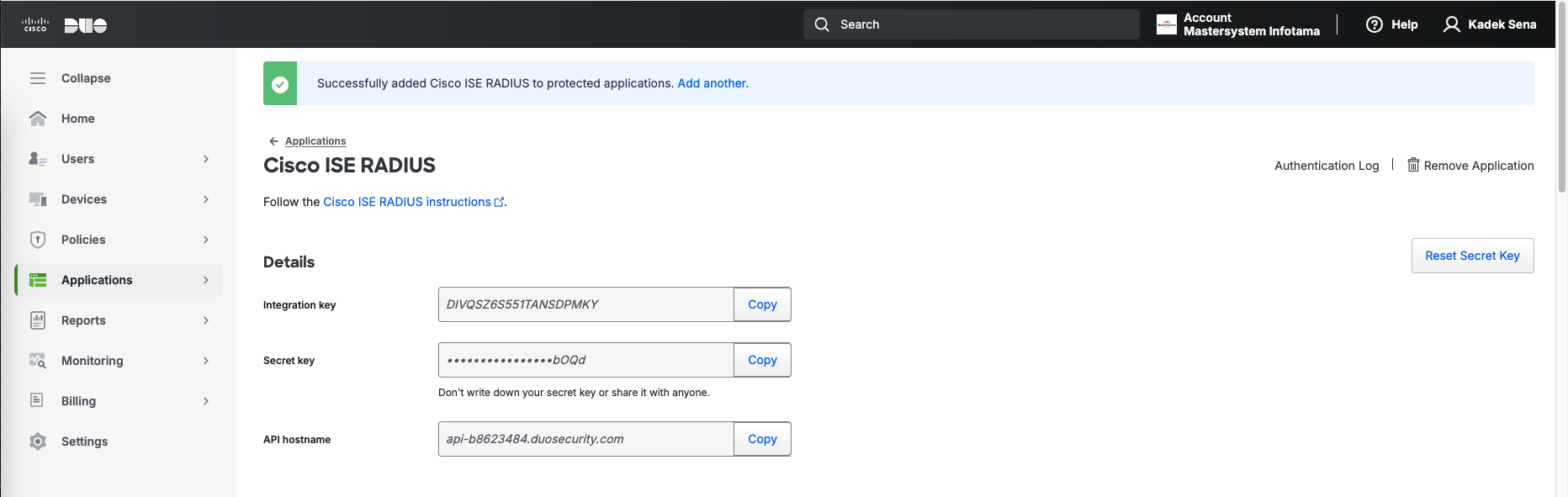
Take notes of the configuration values provided here
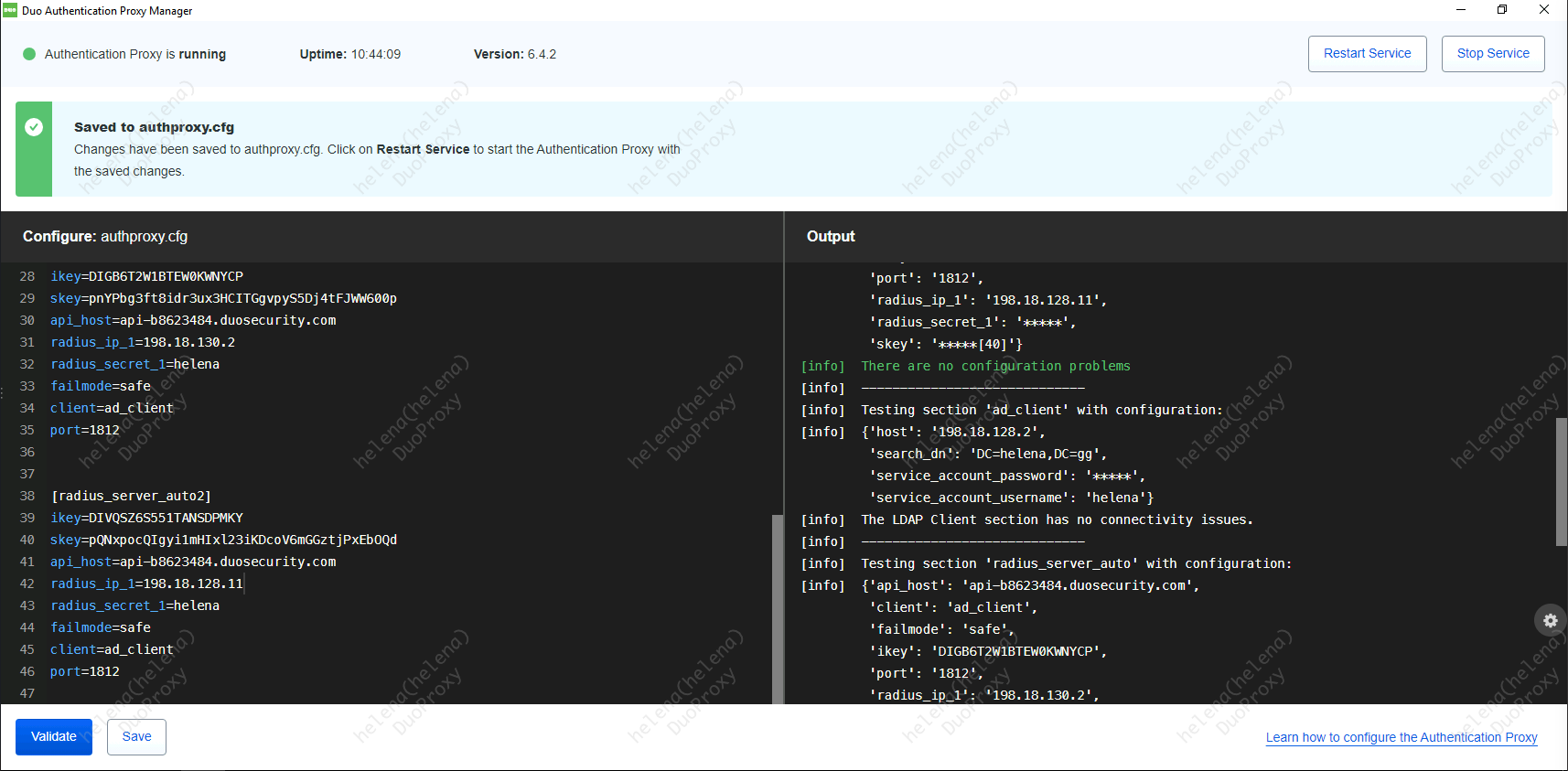
And paste it below the ASA configuration, hit save and restart the service
ISE
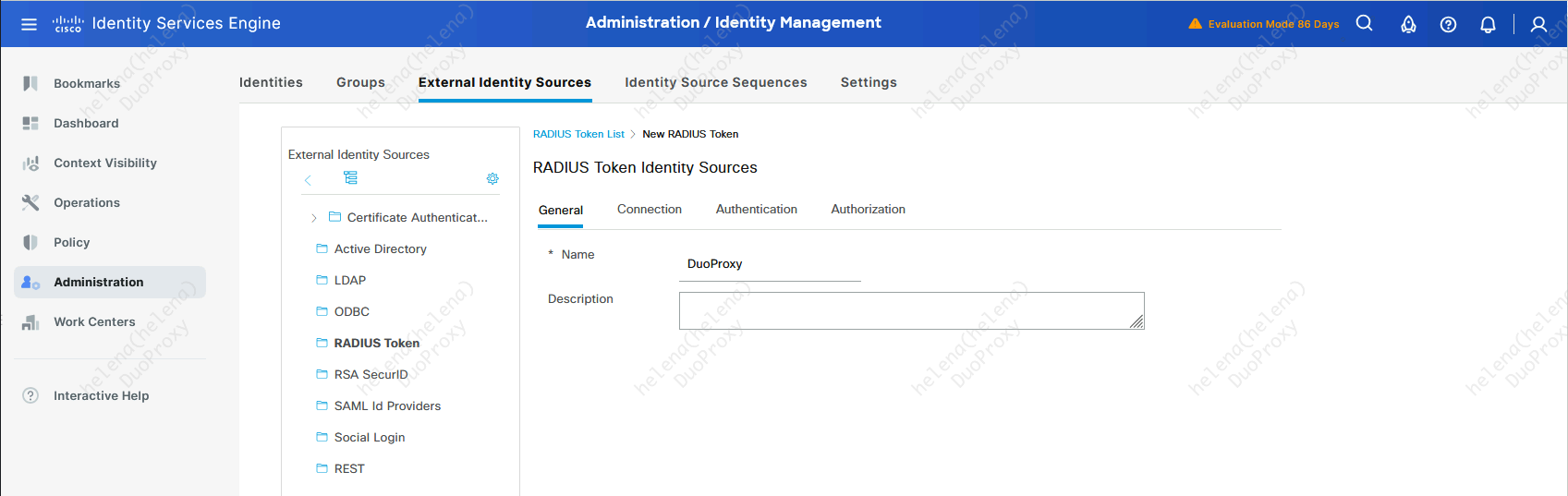
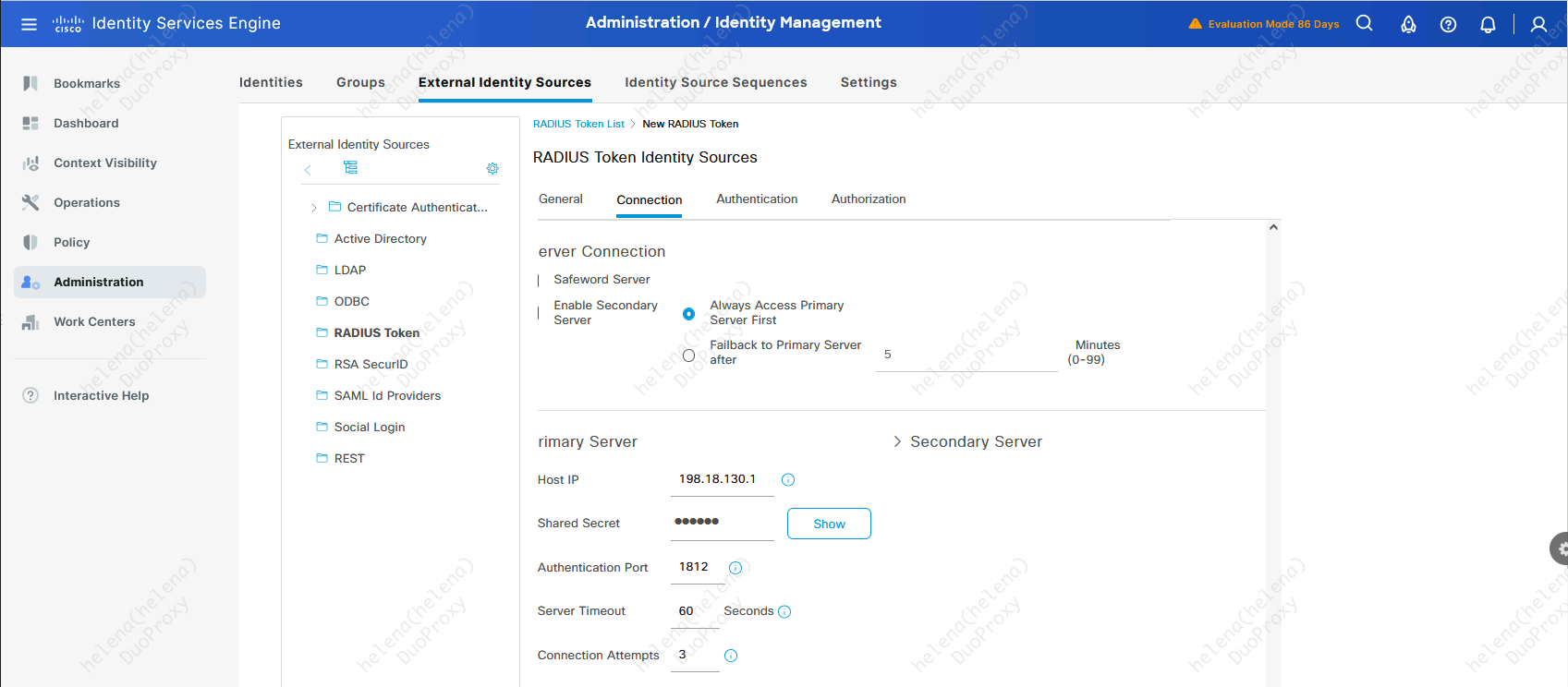
On Cisco ISE, we add a new External Identity Source of RADIUS Token
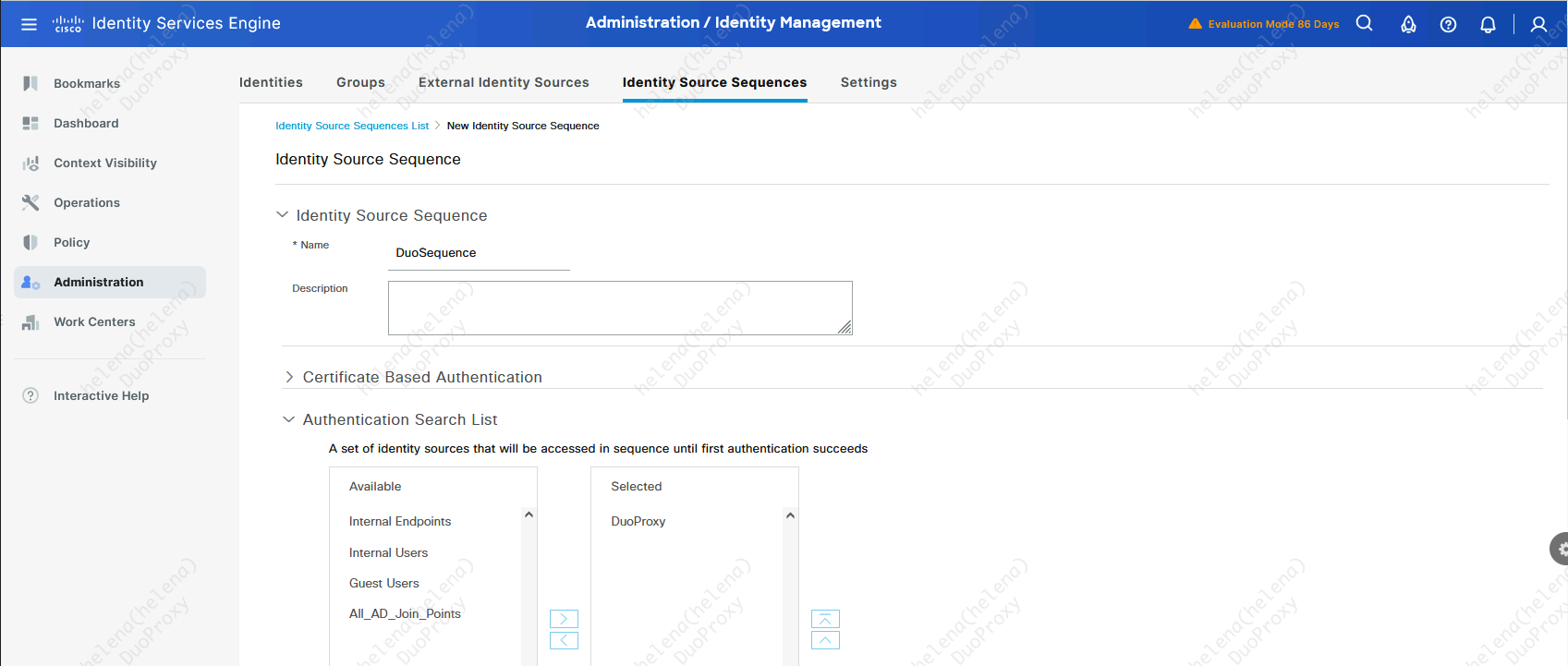
Then add the source into an Identity Source Sequences
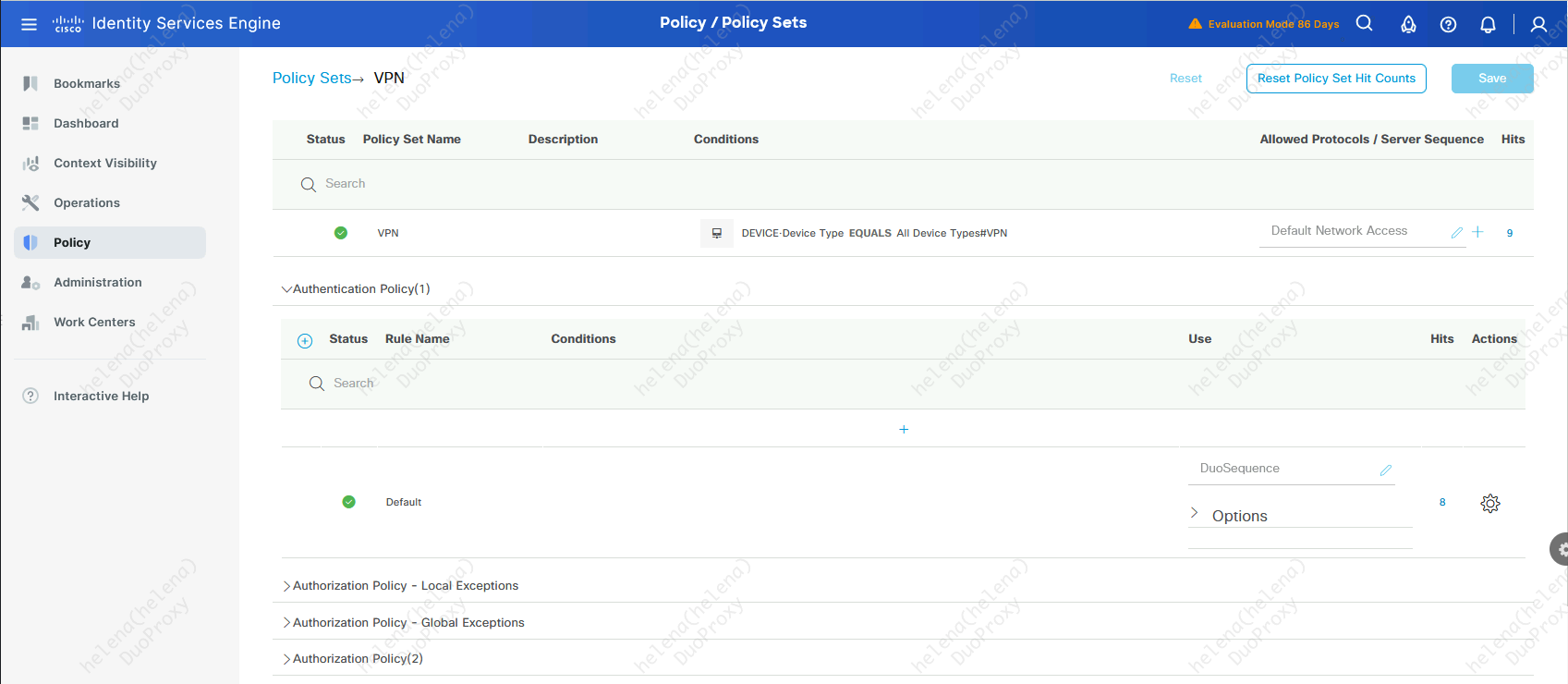
Now we can use this sequence on the Authentication Profile within the RADIUS Policy Set
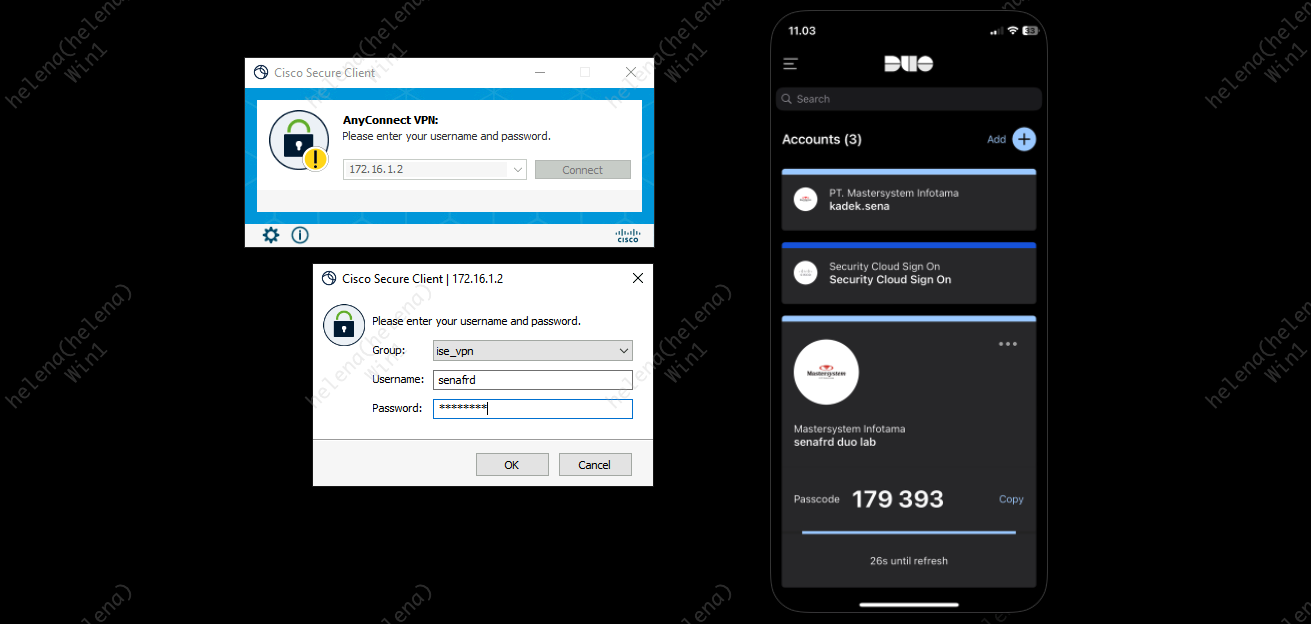
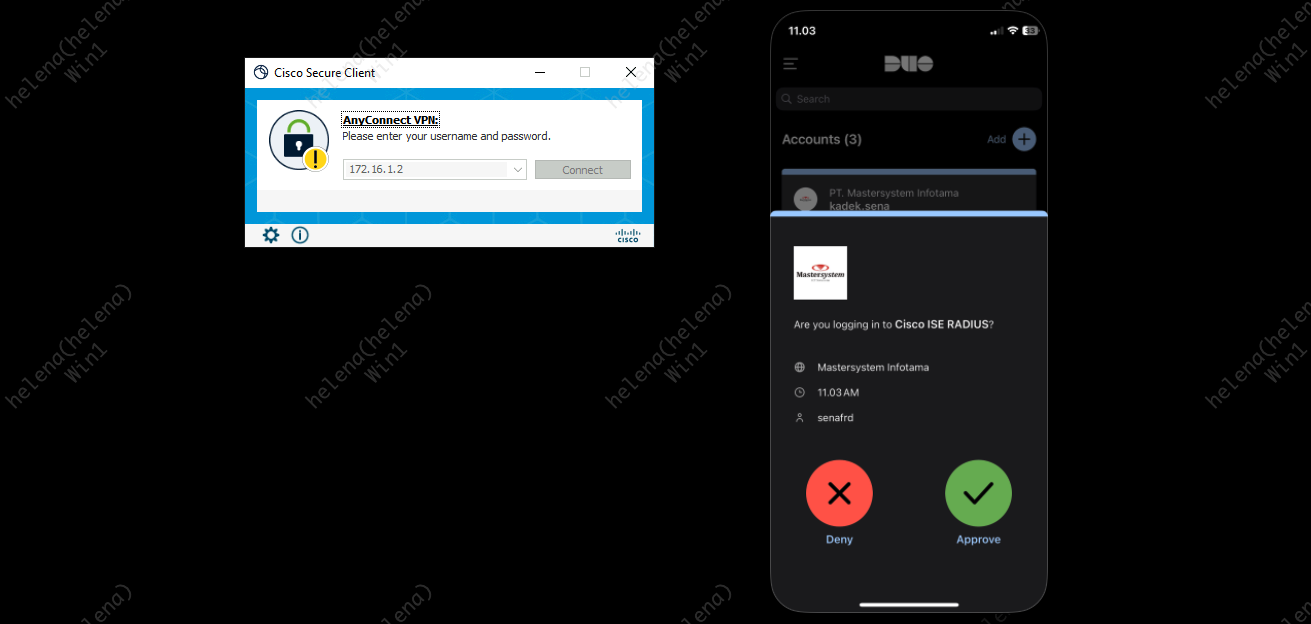
When we hit the Policy Set rule, we will get a MFA confirmation on the Cisco Duo Mobile App
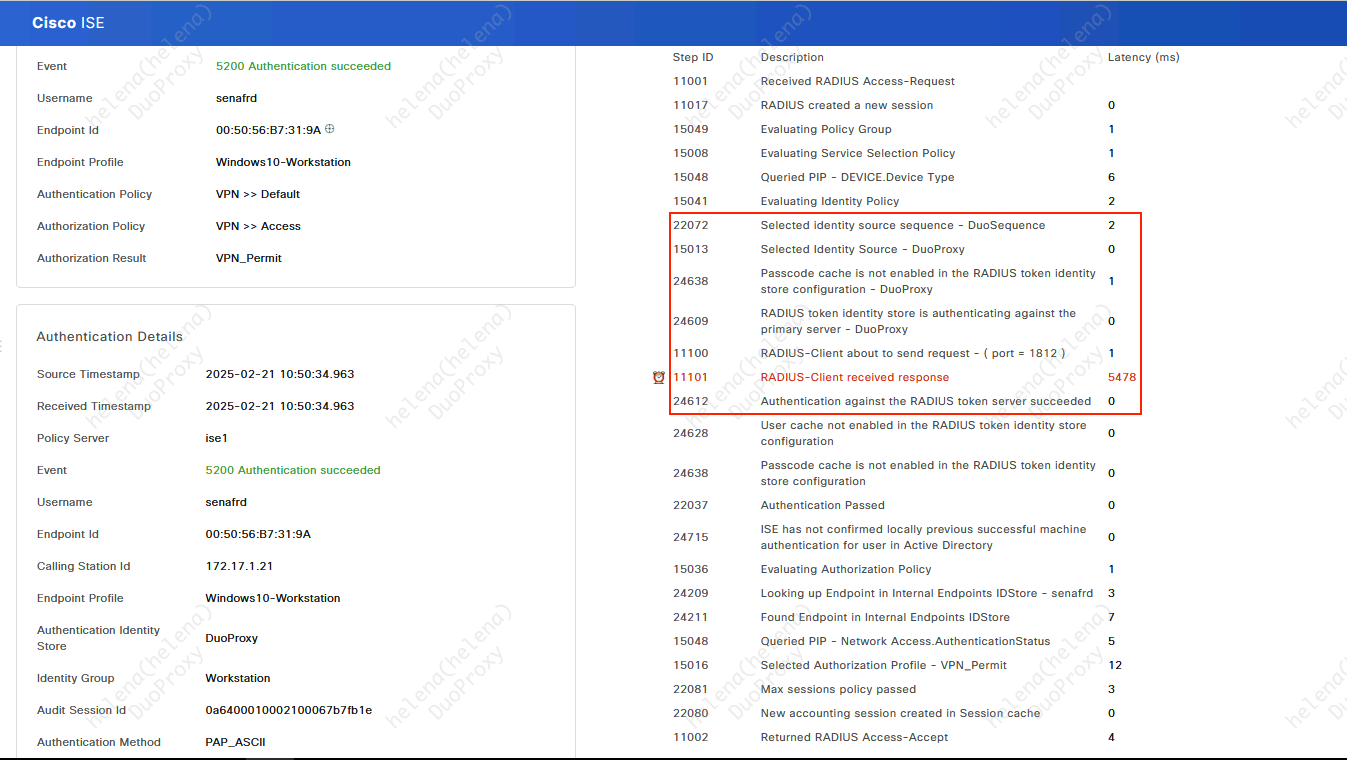
On the Radius Live Logs Details, we can see that the ISE uses the Duo Proxy as the Identity Source for Authentication
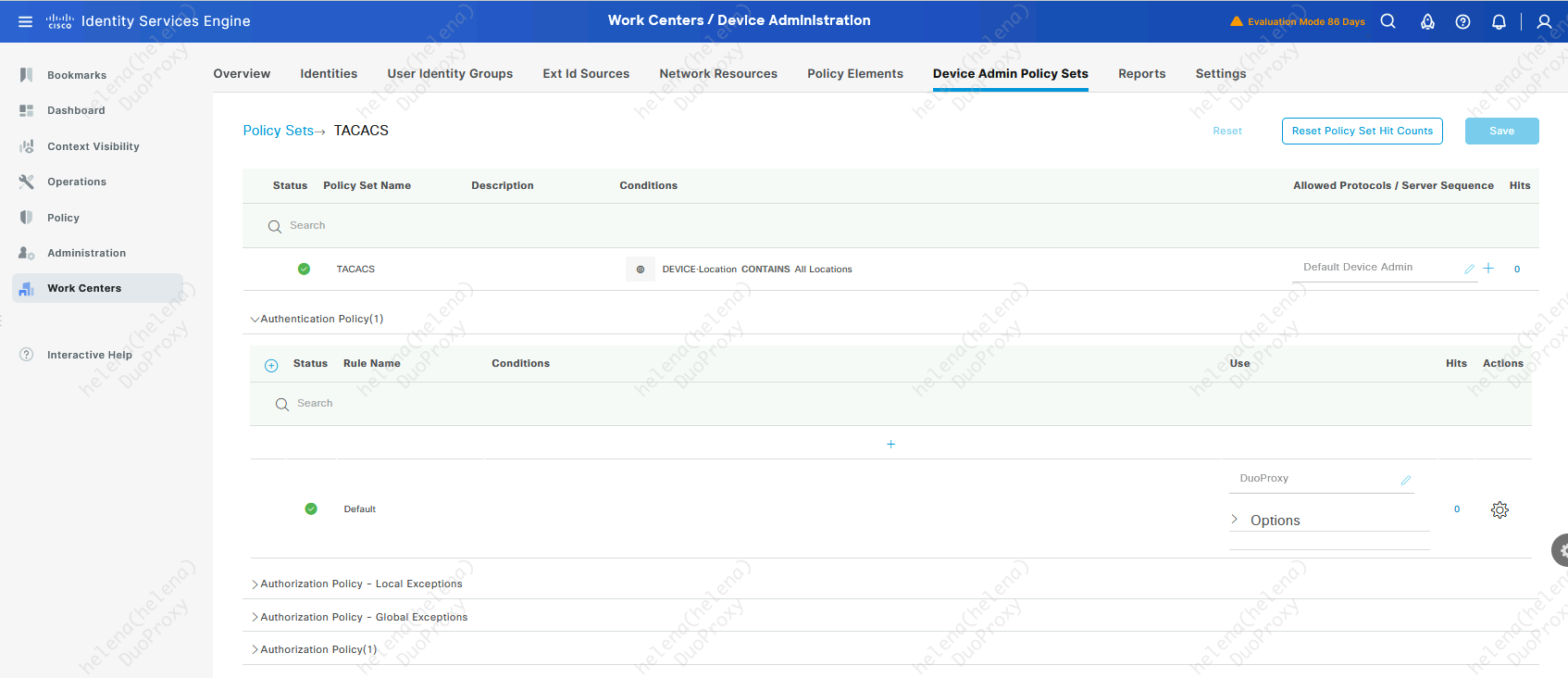
Other than for Network Access, we can also use Duo for Device Admin (TACACS), here we use the Identity Source on the Authentication of a TACACS Policy Set
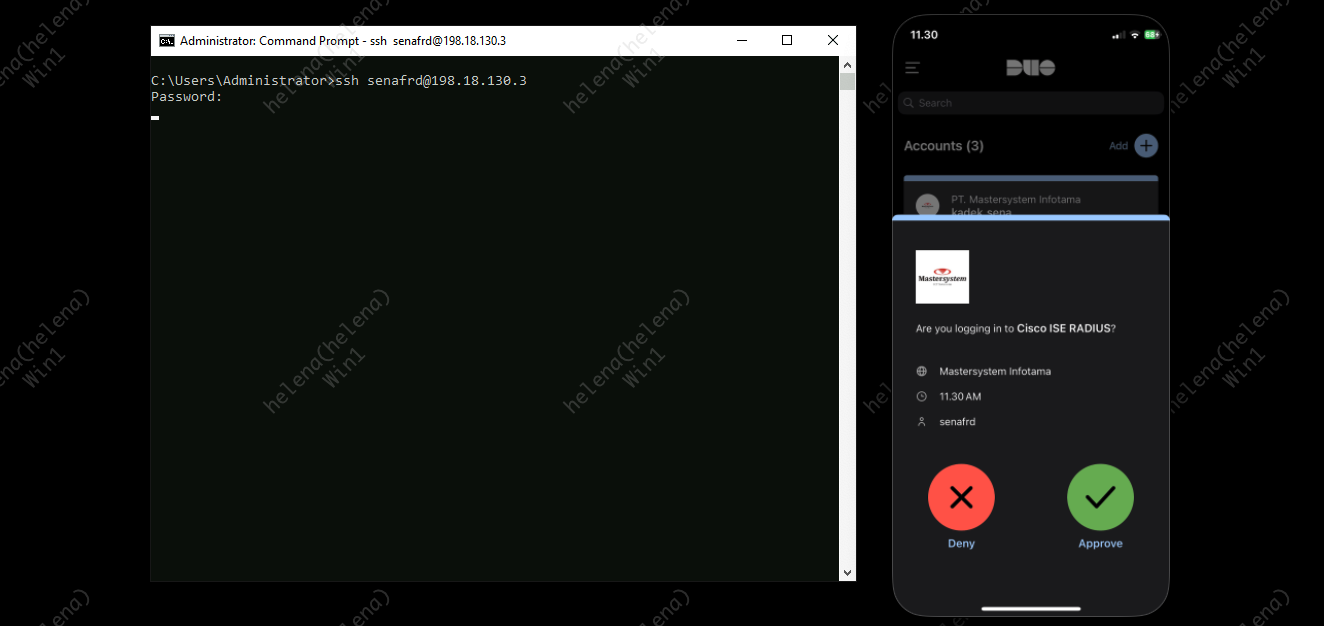
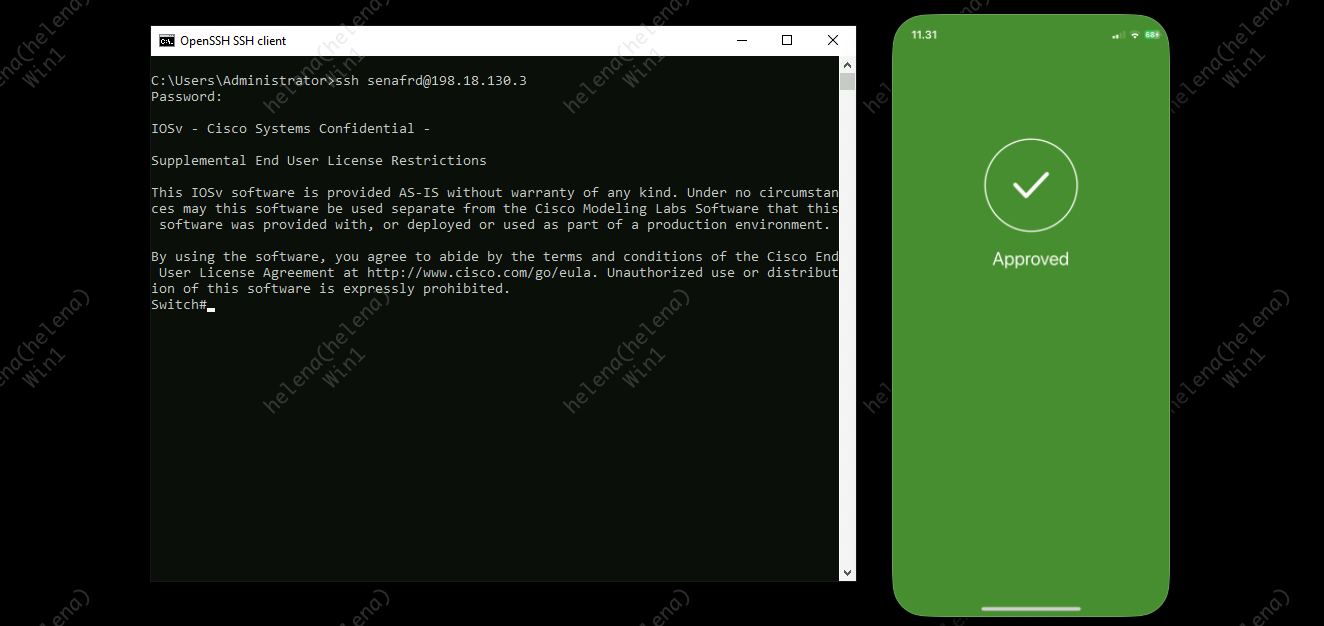
When we try to access the network device, we’ll get a MFA cofirmation on the App
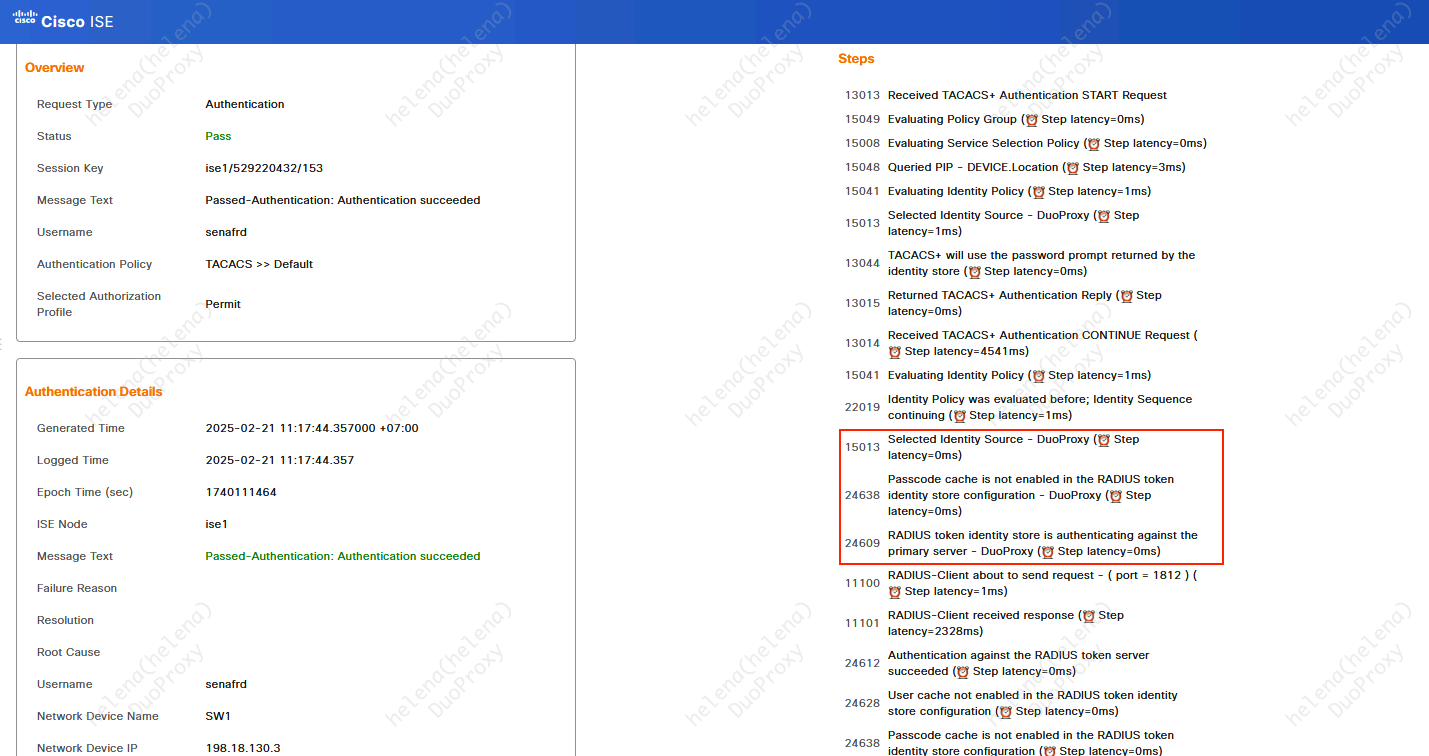
The TACACS Live Logs shows that we’re authenticating against a Duo Proxy Identity Source